esChecker is a Mobile Application Security Testing (MAST) solution built by eShard, a French cybersecurity company based in Pessac, France. The platform performs static, dynamic, and stress testing on Android and iOS mobile app binaries.
eShard describes esChecker as “the fastest and most effective way to prevent security regressions” across mobile application releases.
What is esChecker?
esChecker is powered by a DAST (Dynamic Application Security Testing) engine with IAST (Interactive Application Security Testing) capabilities. You upload your Android or iOS binary, and the platform runs security diagnostics aligned with OWASP MASVS and MASTG test cases.
The platform is designed for pre-production verification — teams run security tests before each release to catch regressions and new vulnerabilities. Results come with actionable remediation checklists.
eShard is primarily known for hardware security testing (chip side-channel attacks, fault injection) and binary analysis. esChecker brings that binary analysis expertise to mobile application security. Their customer base includes organizations like Thales, Visa, NXP Semiconductors, and DBS Bank, though it’s unclear which customers specifically use esChecker versus eShard’s hardware security products.
Key Features
| Feature | Details |
|---|---|
| Testing Types | DAST engine with IAST capabilities |
| Analysis Modes | Static, dynamic, and stress testing |
| Platforms | Android, iOS (binary upload) |
| Standards | OWASP MASVS, OWASP MASTG test cases |
| Output | Remediation checklists, PDF reports |
| Collaboration | Multi-user platform |
| Trial | Free trial available on request |
OWASP MASVS Testing
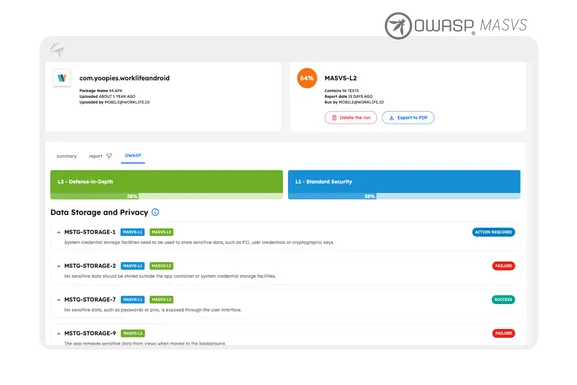
The screenshot from eShard’s official site shows esChecker’s OWASP view, where each MASTG test case (like MSTG-STORAGE-1, MSTG-STORAGE-2, etc.) is evaluated against MASVS levels L1 (Standard Security) and L2 (Defense-in-Depth). Results show clear pass/fail/action-required status for each test.

DevSecOps Integration
eShard positions esChecker as part of the DevSecOps pipeline, running security checks during the development cycle rather than only at the end.

Getting Started
When to Use esChecker
esChecker fits teams that need OWASP MASVS-aligned mobile security testing as part of their pre-release process.
Consider esChecker when:
- OWASP MASVS compliance is a requirement for your mobile apps
- You need to prevent security regressions between releases
- Your team wants a collaborative platform for security assessments
- You value the combination of DAST and IAST analysis
esChecker has limited public documentation compared to larger mobile security platforms. For teams that need a well-documented open-source starting point, MobSF offers free static and dynamic analysis.
See the full mobile security tools category for all options.