Pentest-Tools.com is a cloud-based penetration testing platform that bundles 20+ security tools into a single web interface. Reconnaissance, vulnerability scanning, exploitation, and reporting without installing anything locally.
The platform wraps well-known open-source tools (Nmap, OpenVAS, WPScan, SQLMap, ZAP) in a managed cloud environment and adds automation through what it calls Pentest Robots.
| Feature | Details |
|---|---|
| Deployment | Cloud SaaS |
| Tool count | 20+ integrated tools |
| Recon tools | Subdomain discovery, port scanning (Nmap), Google dorking, DNS analysis |
| Web scanners | SQLi, XSS, command injection, directory traversal |
| CMS scanners | WordPress (WPScan), Drupal, Joomla, SharePoint |
| Network scanner | OpenVAS |
| Exploitation | SQLMap, Sniper auto-exploiter, XSS PoC generator |
| Automation | Pentest Robots (chained tool workflows) |
| Reports | Customizable DOCX templates |
| SSL/TLS | POODLE, Heartbleed, ROBOT detection |
What is Pentest-Tools.com?
According to the OWASP Testing Guide, a thorough web security assessment involves reconnaissance, vulnerability scanning, and exploitation in sequence.
The platform aims to replace the workflow of switching between a dozen different CLI tools during a penetration test.
You add a target, pick the tools you need, and run them from a browser.
Results aggregate in one place, and you can generate a report when done.
It is not a single-purpose DAST tool . It is closer to a pentest workbench that includes DAST capabilities alongside network scanning, recon, and exploitation features.
What are Pentest Tools’s key features?
Tool categories
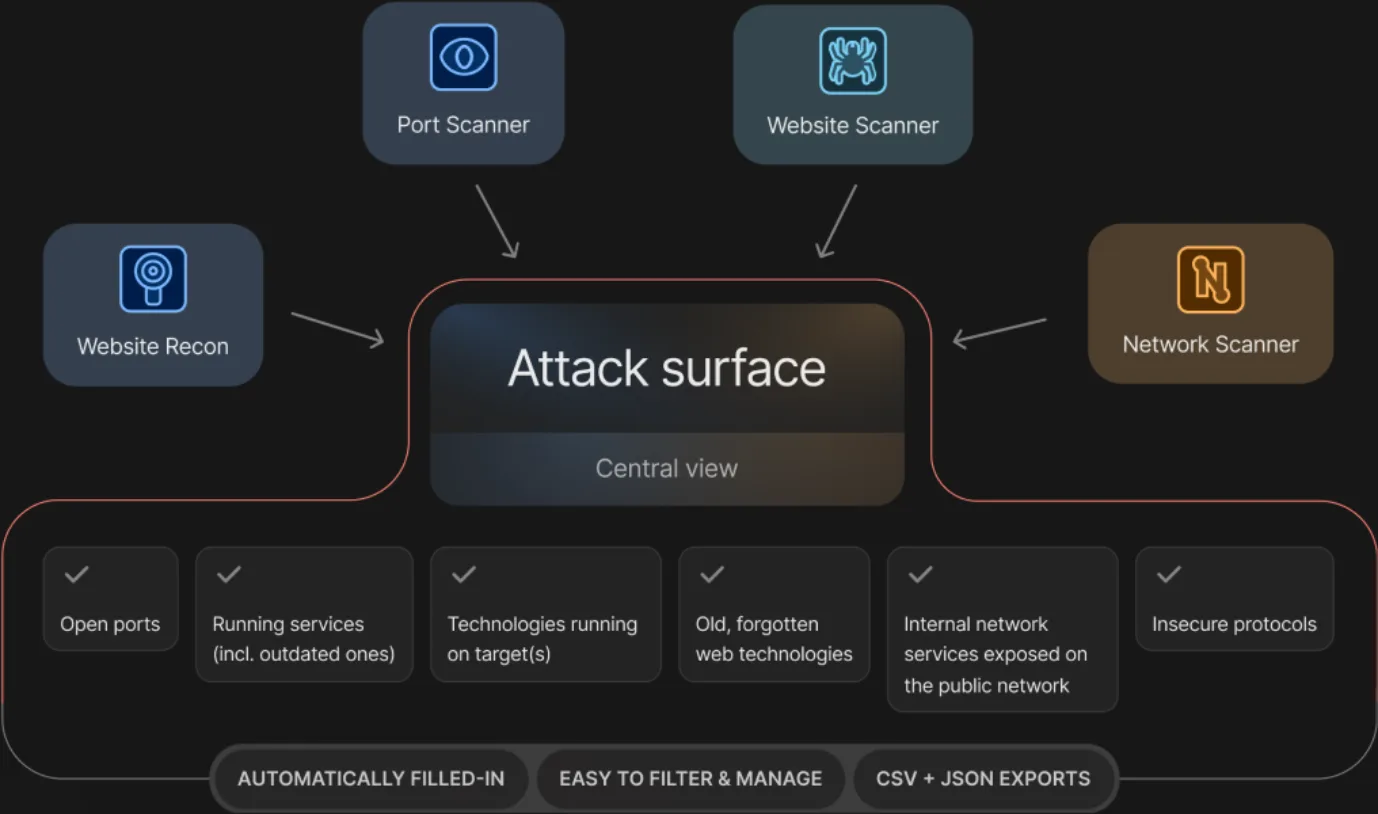
Reconnaissance
- Google Hacking — discovers indexed information about targets
- Subdomain Discovery — maps subdomains via DNS and web scraping
- Port Scanning — TCP/UDP discovery via Nmap integration
- Web Technology Detection — identifies server and client-side tech stacks
- Domain Association — finds related domains and properties
- Virtual Host Discovery — locates multiple sites on single IPs
Vulnerability scanning
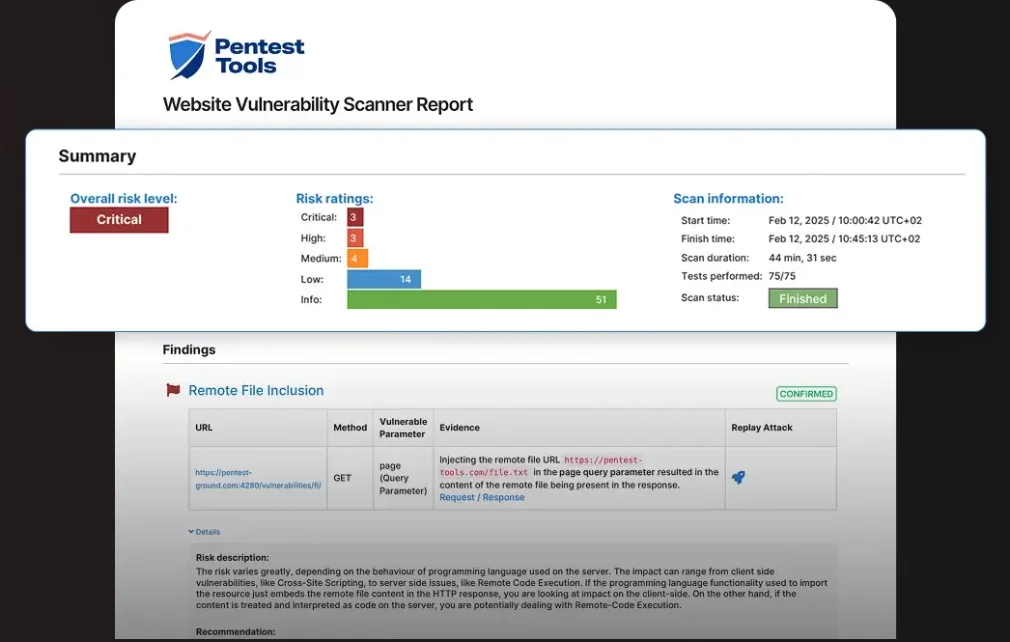
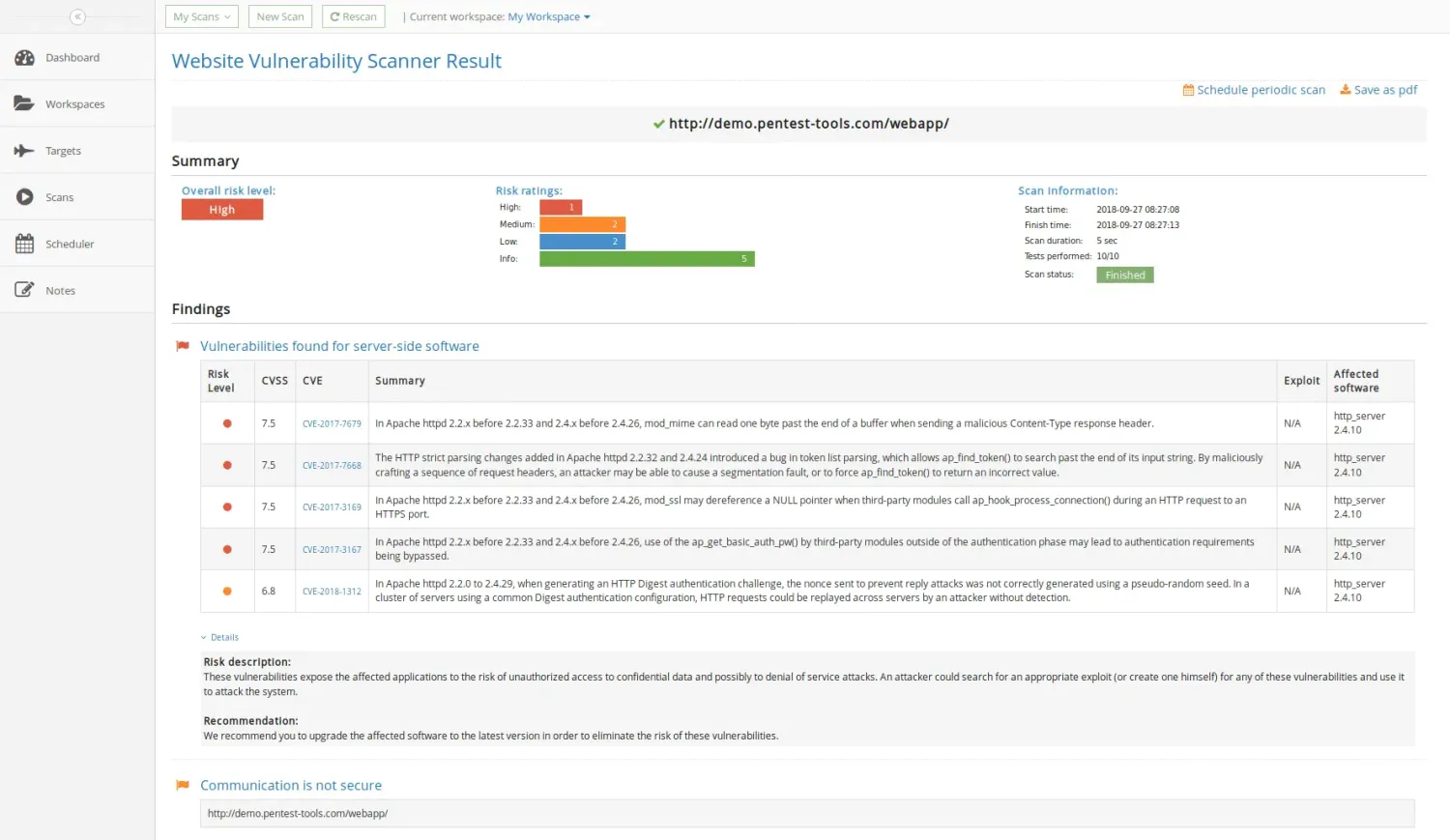
- Website Scanner — SQL injection, XSS, command injection, directory traversal (covering OWASP Top 10 categories A03:Injection and A07:Cross-Site Scripting)
- XSS Scanner — dedicated cross-site scripting detection (ZAP-powered)
- SQL Injection Scanner — deep web inspection for SQLi
- Network Scanner — OpenVAS integration for infrastructure CVEs
- SSL/TLS Scanner — protocol and cipher configuration checks
Exploitation
- Sniper Auto-Exploiter — automated exploitation of known vulnerabilities
- Password Auditor — weak credential testing
- URL Fuzzer — hidden content and directory discovery
- SQLi Exploiter — SQL injection exploitation via SQLMap
- XSS PoC Generator — proof-of-concept generation for confirmed XSS
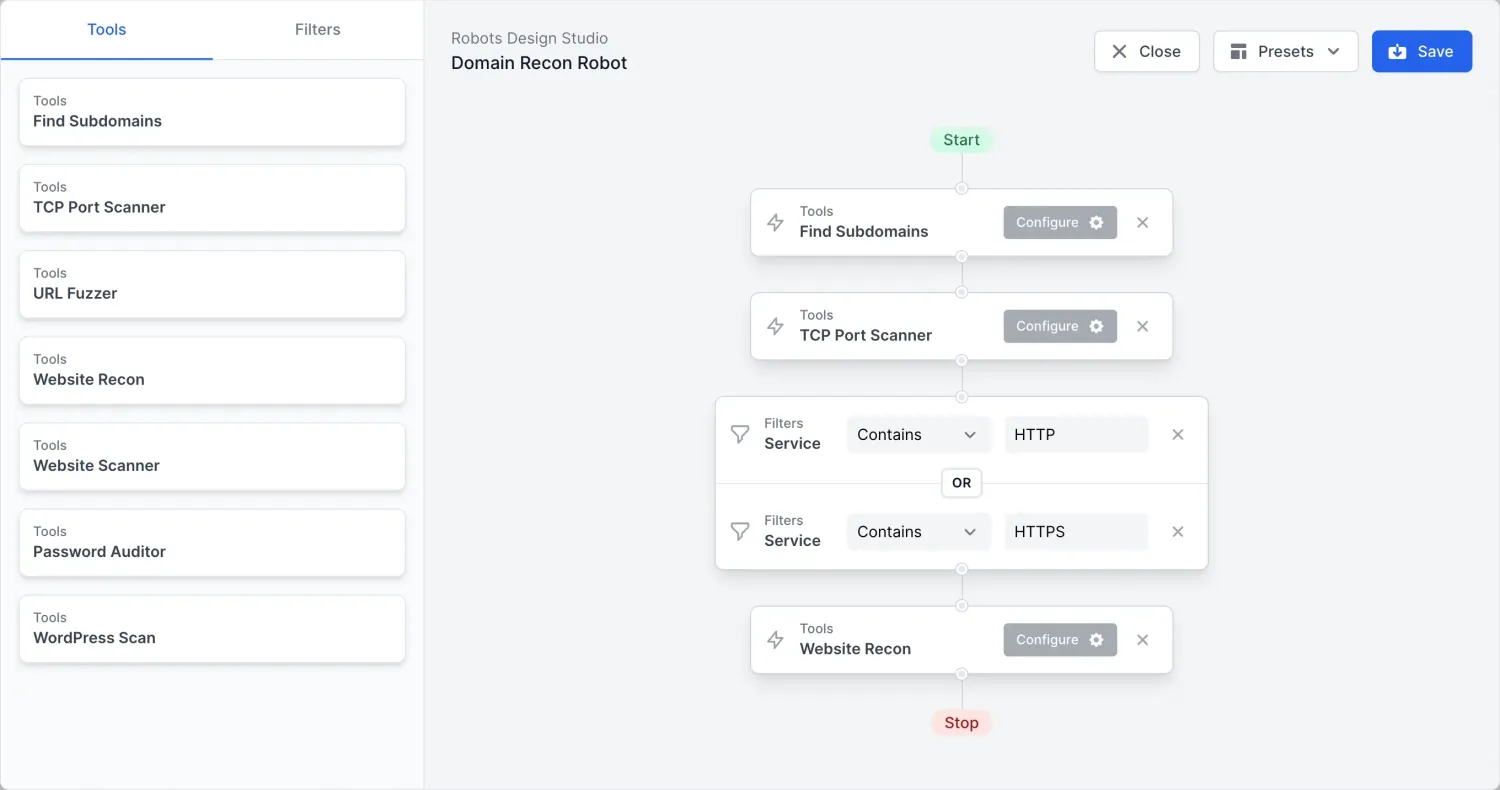
How do I get started with Pentest Tools?
When to use Pentest-Tools.com
The platform is a good fit for pentest consultants who want cloud-hosted tools without local setup.
It also suits teams that need a unified interface across recon, scanning, and exploitation phases, and organizations that want professional DOCX reports without manual formatting.
It is less suitable if you need deep control over individual tool configurations, want to run everything on your own infrastructure, or need specialized testing (API security, mobile) beyond what the bundled tools cover.
For dedicated web application security testing, a focused DAST tool like Invicti or Acunetix will likely go deeper on application-level vulnerabilities. Pentest-Tools.com trades depth for breadth.
If you only need web vulnerability scanning, check the free DAST tools guide or consider Nikto for lightweight server-level checks.
Pentest-Tools.com pricing
Pentest-Tools.com publishes pricing publicly on pentest-tools.com/pricing — one of the few platforms in this category that does not gate quotes behind a sales call.
The current plan structure (as of April 2026) is workflow-shaped rather than seat-shaped:
- NetSec — network vulnerability assessment and attack surface discovery, starting at $79/month on the annual save-2-months promo (list price ~$95/month).
- WebNetSec — adds web vulnerability scanning on top of NetSec for full-stack coverage.
- Higher tiers — add capabilities like continuous scanning, Pentest Robots automation, advanced reporting, and team collaboration.
- Enterprise — custom pricing for organizations with more than 500 assets, contacted directly.
Verify the live tier-and-price layout on pentest-tools.com/pricing — Pentest-Tools.com refines the lineup periodically and add-ons can move between tiers. A free tier with limited usage is also available for testing the platform before subscribing.
Pentest-Tools.com alternatives
If Pentest-Tools.com’s bundled-toolkit model is the wrong fit, four alternatives cover most adjacent buyer shapes:
- Intruder — cloud vulnerability scanner with automatic discovery of new assets, AWS/Azure/GCP connectors, and continuous monitoring. Better for ongoing infrastructure-focused vulnerability management than ad-hoc pentest engagements.
- Detectify — continuous attack-surface scanning with crowd-sourced research from ethical hackers. Strong for SaaS companies that want hands-off external testing rather than building a pentest workflow themselves.
- Nuclei — free, open-source template-driven scanner with 12,000+ community YAML templates. Right when you want full control, custom checks, and CI/CD-native scanning without a SaaS subscription.
- Burp Suite Professional — manual web pentesting toolkit with intercepting proxy, Repeater, Intruder, and 500+ extensions. Better than Pentest-Tools.com when human-driven exploration of single applications is the primary workflow.
For more options, browse the DAST tools directory on AppSec Santa.








